The Capabilities of Surveillance Devices
01.06.2017 - With the Internet of Things (IoT) growing in use across cameras, appliances, industrial machinery, vehicles, and smart home technology, malware has many more devices to both target...
With the Internet of Things (IoT) growing in use across cameras, appliances, industrial machinery, vehicles, and smart home technology, malware has many more devices to both target and launch cyber-attacks from than ever before. Consequently, a major concern of the industry grounds on reoccurring cyber-attacks.
The sophistication of cyber-attacks and the types of devices involved are both increasing in number and evolving in complexity. Instead of traditional IT devices, a lot of attacks target network cameras and digital video recorders – loose ends of a security system. Transforming those devises into robotic attackers or “bots” by
an infection of Mirai malware, they were generating Distributed Denial of Service (DDoS) attacks, keeping the targeted websites so busy that they were unable to respond to legitimate user requests.
In October 2016, a well-publicized DDoS attack impacted up to 85 web services for an eleven-hour period. Users across parts of North America and Europe were unable to access Amazon, the Financial Times, Netflix, PayPal, Reddit, Spotify, Twitter, and several other well-known services. Beyond the impact on user convenience, an estimated $100M USD loss in revenue resulted from the attack, leading to both the FBI and Homeland Security became involved in the investigation. It is crucial that the security industry is committed to providing cyber security protection. Arecont Vision for example focuses on the cyber security for their IP network cameras, and they inform about unique cyber benefits of their cameras, the nature of the attacks, and recommendations for our customers.
The Challenge for Security Manufacturers
Many manufacturers of security cameras have typically considered their products to be edge devices, relying on the IT department to provide the necessary network protection, limiting access only to those authorized while excluding external threats.
Today more manufacturers and their customers are aware that anything connected to the network requires cyber security protection.
One challenge for manufacturers of network-enabled security products is to balance ease of installation and ongoing operation with the protection of the device, the network, and the connected infrastructure.
A product with extremely strong cyber security protection may turn away customers by being too restrictive or complex for their needs when
setting up or during ongoing operation. Equally important, a product that is exceptionally easy to setup and administer may be a gateway to cyber-attack. Finding the balance between these two factors while meeting the requirements of IT is a challenge to be solved by manufacturers since not every organization has identical needs.
Arecont Vision addresses this challenge with user IDs/passwords and their own in-house designed architecture. Their cameras feature the ability to set user IDs and 16 digit ASCII passwords (use of which is recommended) for basic cyber security, and they provide systems integrator and customer training on best security practices through Arecont Vision University.
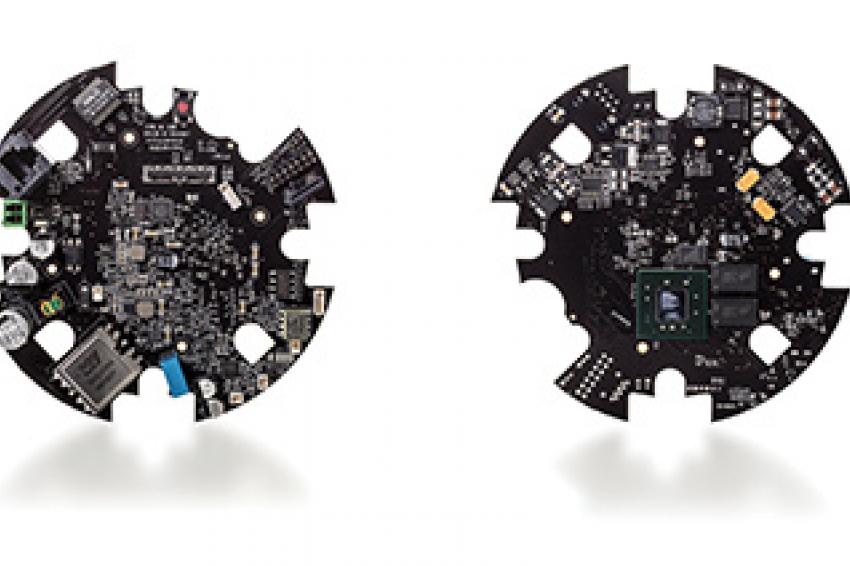
As further protection, the design of all Arecont Vision cameras differs from competitor offerings. Arecont Vision’s Massively Parallel Image Processing architecture runs on a Field Programmable Gate Array (FPGA) integrated circuit (IC) in each Arecont Vision camera. This ensures that the camera cannot be used as a platform for cyber-attacks.
Considering Cameras
Organizations continue to rely on Arecont Vision cameras to not be hacked and repurposed in cyberattacks on other networked devices. Arecont Vision cameras will therefore continue to balance the user experience with appropriate cyber security, including the recommended use of 16 digit ASCII passwords after the camera is configured for use by the installer. No device should be connected to the network without this capability enabled, including surveillance cameras. Users should be aware that Cameras which cannot be updated with the latest product features and security updates from the manufacturer should not be part of the network and should be replaced. Also, operating systems with known security risks on the camera should not be part of the network and should be replaced.
Customers should employ best practices in cooperation between the IT and security departments for basic cyber security. Having a cyber security
action plan that is tailored to the needs of the organization is important. Employee education is another key to cyber security, and should be a part of ongoing employee development. The Arecont Vision Try-and-Buy program for example ensures to obtain and install an Arecont Vision camera risk free for a trial at the customersite.
To find out more about Arecont’s cameras and latest ideas about Cyber Security, check out their whitepaper, which provides further information
on their products: www.arecontvision.com/whitepapers/#
Contact
Arecont Vision Costar
400 N Brand Blvd., Suite 860
Glendale, CA 91203
+1 818 937 0700
+1 818 937 0464